An Analysis of Omise’s Bug Bounty Program
We recently passed the one year anniversary of the public launch of our bug bounty program on the HackerOne platform. After a year of using this program, we look back and analyze whether it was successful or not, and also share what we have learned by working with the community to improve Omise security.
What Is a Bug Bounty Program?
On the internet today, there are individuals and (some state-sponsored) people that would like to do harm to businesses. They spend a lot of time trying to find weaknesses to exploit companies and their services.
Luckily enough, there are also ethical people out there researching security issues. Unlike the bad guys, these people report the weaknesses they find in a responsible way. A bug bounty program is set up for the good guys and makes it possible to give them a reward for their efforts.
Omise’s Bug Bounty Program
Omise has been using the HackerOne platform for its bug bounty program since the start. However, we were using it in a private mode, working with a selected few external security researchers.
While this was beneficial for us, we were not yet ready to go public as we did not have the correct procedures to handle submissions from everyone. Then one year ago, we finally felt ready and did it. We launched our bug bounty program to the public.
Now security researchers can report issues on https://hackerone.com/omise.
Once we receive a reported issue, the Omise security team will triage the report and verify if it is valid. Then we work with engineering teams to prioritize, implement and deploy a fix.
Once the fix has been deployed, we give the security researcher a reward.
Issues
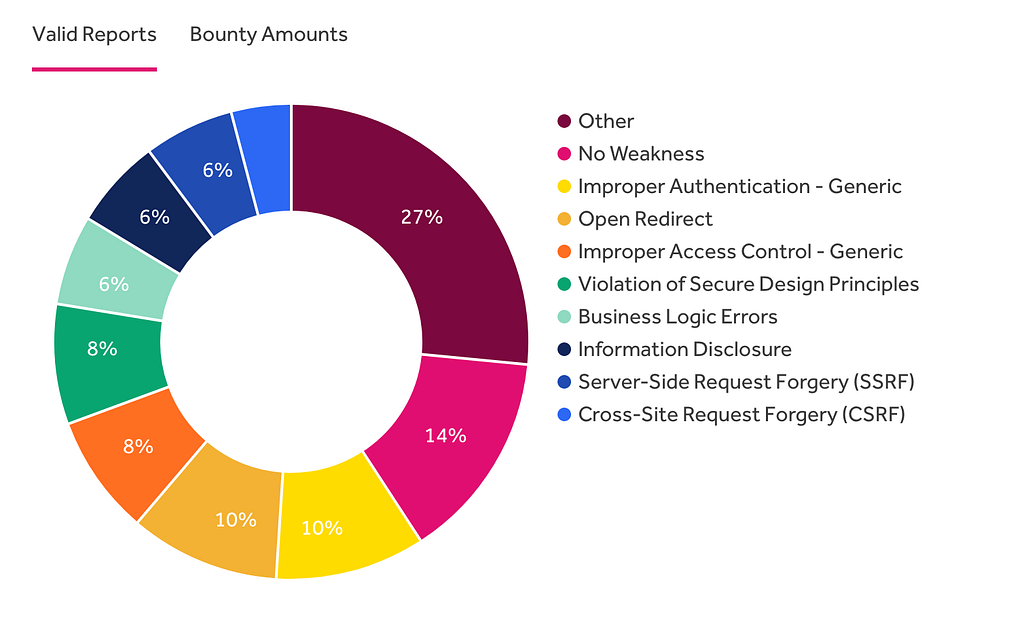
Since we went public a year ago, we received 60 valid issues of varying severity. The largest amount of issues found was on our web dashboard. We also received multiple issues on a broad selection of assets we have, such as our API, libraries, and SDKs hosted on https://github.com/omise
After we launched our program to public security researchers, these are the types of issues that we found:
A Close Call
While the majority of the issues have not been critical, there was one memorable issue that could have turned really bad under the correct circumstances.
In our dashboard, we have the functionality to send notifications to our merchants using ‘webhooks’. This functionality had an issue that allowed calls to be made not only to our merchants’ websites but also to our own internal resources. This would result in displaying information received through webhooks on the dashboard which could allow sensitive data to be exposed to a potential attacker. While this information was partially masked, the consequences could still have been really bad.
We investigated the issue immediately, making sure that no one had exploited this vulnerability and released a fix. If this issue had been found by a malicious attacker, Omise could have been at risk for both financial and reputational costs.
At Omise, our engineering team always aims to deliver the highest quality software possible. In the worst case that a security or reliability issue is discovered, it will have the highest priority until fixed.
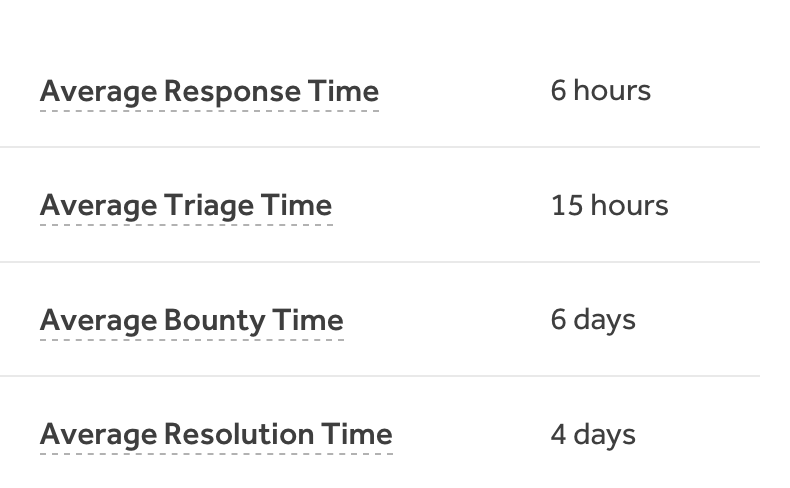
Here are our statistics for responding to security issues in the past year:
What Have We Learned?
The bug bounty program has made us improve on our security incident handling procedures. We have also received insight into products and why they might have had issues in the past.
We included more of our assets into the bug bounty program and learned how to be better at testing for security issues.
Summary
We are pleasantly surprised by how good the bug bounty program has been working for us. The level of expertise out there in the community is amazing! They have provided us with better security insights and have found really hard-to-discover issues in all sorts of crazy ways.
We are committed to continue working with the community and welcome anyone to visit our program at https://hackerone.com/omise.
We would like to thank all the researchers over the past year. Thank you, you have made Omise more secure.
More from us
Thank you!
You are subscribed.